The digital transformation of the modern enterprise has reached a point where a single misplaced click or a sophisticated social engineering scheme can vanish decades of corporate intelligence into the ether within seconds. While the migration from dusty on-premises server rooms to the sleek efficiency of Software-as-a-Service (SaaS) platforms was marketed as a panacea for IT headaches, it has inadvertently birthed a massive accountability gap. Organizations often operate under a comfortable but fundamentally incorrect assumption that cloud-native data is inherently shielded from disaster. This misplaced trust creates a scenario where platform uptime is mistaken for comprehensive data protection, leaving businesses vulnerable to a reality they are rarely prepared to face.
The High Cost of Misplaced Trust in the Cloud
Many organizations navigate their daily operations with a sense of security that is more atmospheric than actual, believing that because their tools are managed by global tech giants, their information is immortal. However, the shift to SaaS has not eliminated risk; it has simply changed its shape and hidden it behind a curtain of subscription fees and user-friendly interfaces. If a critical file is accidentally deleted during a routine sync or if a ransomware attack encrypts an entire CRM database tomorrow, the burden of recovery does not fall on the provider. Instead, it rests entirely on the shoulders of the customer who, in many cases, has no secondary copy of that information.
This disconnect between expectation and reality often leads to catastrophic operational paralysis when the unexpected occurs. Statistics from recent industry surveys underscore the severity of this issue, with a staggering 87% of IT professionals reporting significant SaaS data loss within the last year. Despite these numbers, executive leadership frequently remains unaware that their primary service providers are not acting as digital insurers. When the “water” flowing through the cloud pipes becomes contaminated or runs dry, the provider ensures the pipes are still standing, but they offer no guarantees regarding the liquid they carry.
Defining the Boundary Between Vendor Uptime and Data Ownership
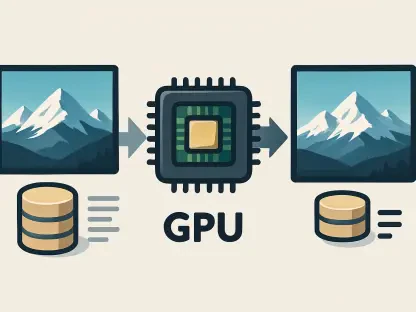
The cornerstone of modern cloud security is a framework known as the Shared Responsibility Model, which clearly delineates the duties of the provider versus those of the customer. In this structured relationship, industry leaders like Microsoft, Salesforce, and Google take responsibility for the “infrastructure” of the service. They ensure that the application is available 24/7, that the underlying hardware is patched against vulnerabilities, and that the physical data centers are guarded against intrusion. They are responsible for the availability of the service, but they are explicitly not responsible for the integrity or the preservation of the user data itself.
Under the legal terms of nearly every major SaaS agreement, the customer remains the sole owner and protector of their data. This means that if information is corrupted by a faulty third-party integration, wiped out by a disgruntled employee, or held hostage by an external hacking group, the vendor is legally and operationally insulated from the loss. The provider’s role is to maintain the stage; what the actors do with their scripts is entirely up to the theater company. Recognizing this boundary is the first step toward moving away from a passive security posture toward one of active resilience.
Deconstructing the Risks of Relying Solely on Native Tools
Relying on a vendor’s basic recycle bin or internal versioning system is not a backup strategy; it is a temporary safety net with a dangerously short fuse. Most SaaS providers offer very limited retention windows, which often range from a mere 14 to 93 days depending on the specific license and application. Once this period expires, the data is purged from the provider’s systems forever, leaving no trail for recovery. This creates a massive vulnerability for organizations that may not discover a data breach or a silent corruption event until months after it has occurred.
The risks are not merely theoretical, as evidenced by large-scale social engineering attacks that have successfully bypassed platform-level security to extract or delete billions of records from reputable CRMs. These incidents demonstrate that even the most robust platforms are susceptible to human-centric vulnerabilities that bypass traditional encryption and firewalls. When an attacker gains legitimate administrative credentials through deception, the platform treats their destructive actions as authorized commands. Without an independent, off-site copy of that data, the organization has no “undo” button for the damage caused by a compromised internal account.
Navigating the Regulatory and Operational Impact of Data Loss
Beyond the immediate panic of missing files, inadequate backup strategies carry heavy long-term consequences for corporate governance and legal standing. Research indicates that by 2028, 75% of enterprises will treat SaaS backup as a critical requirement, a massive leap from previous years as boards finally realize that data loss is a strategic failure rather than just a technical glitch. Organizations operating without independent, immutable backups face severe regulatory exposure under global mandates like GDPR and HIPAA. These regulations require specific data retention periods and accessibility standards that native SaaS tools were never designed to meet.
Furthermore, the financial landscape is shifting as cyber insurance providers become increasingly stringent regarding their payout requirements. Many insurance companies are now denying claims to businesses that cannot prove they have verified, off-site recovery procedures in place. It is no longer enough to say that data is “in the cloud”; insurers want to see evidence of a redundant, air-gapped recovery strategy that exists outside the primary production environment. A failure to provide this proof can result in the total loss of coverage, leaving a company to absorb the full financial impact of a data breach or system failure.
A Framework for Building a Resilient SaaS Backup Strategy
To bridge the shared responsibility gap, organizations had to move beyond passive trust and implement a proactive data protection framework. This process began with a thorough audit of commercial licensing terms to identify exactly where the vendor’s protection ended and the company’s began. Leaders then mapped their internal data retention policies to specific legal and operational needs, ensuring that their backup frequency matched the pace of their business. They assigned clear executive ownership over SaaS backup, moving it from a secondary IT task to a core component of the organization’s broader risk management strategy.
The most effective defenses ultimately involved deploying dedicated third-party backup solutions that offered point-in-time restoration and geographically separate storage. These systems ensured that even if a primary SaaS platform suffered a catastrophic event or a regional outage, the business could continue to operate using its independent data repository. By prioritizing immutable backups that were shielded from the primary production environment, organizations finally secured the “water” within their cloud pipes. This transition toward active data stewardship transformed the cloud from a source of hidden risk into a truly resilient foundation for future growth.